Configure PPP (3.3) > Cisco Networking Academy Connecting Networks Companion Guide: Point-to-Point Connections | Cisco Press

Table 1 from Network access authentication infrastructure using EAP-TTLS on diameter EAP application | Semantic Scholar
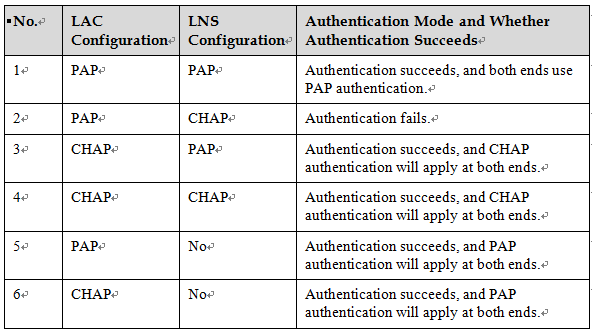
FAQ-In What Cases Can the Non-authentication Mode Be Configured When the PC Dials up to the LNS- Huawei
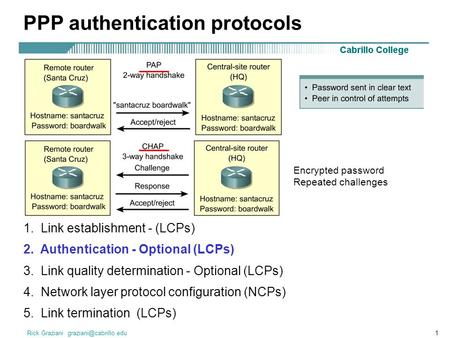
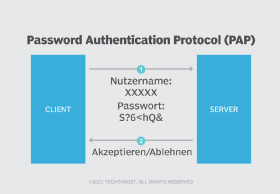
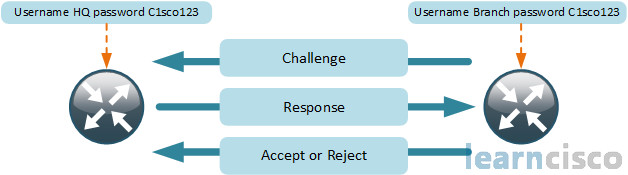
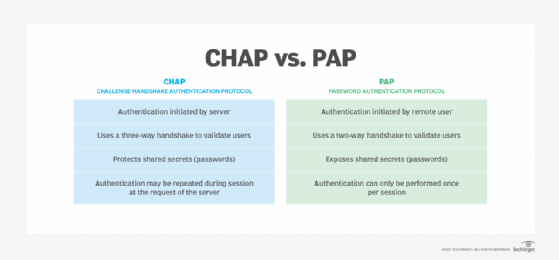
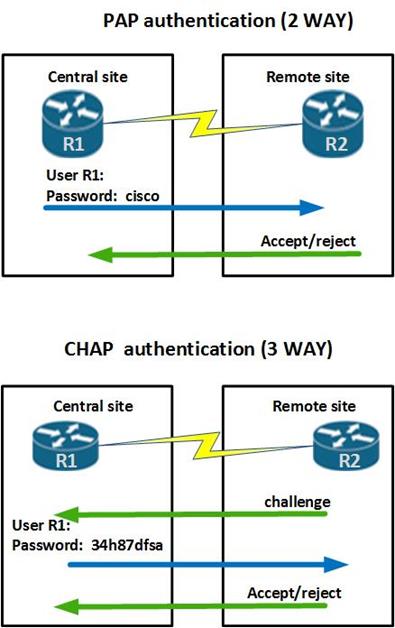
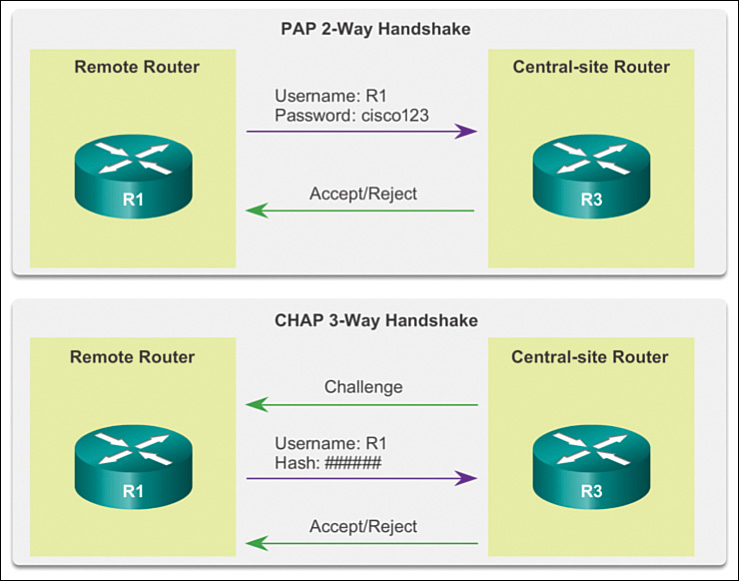
RADIUS Server PAP & CHAP Protocols. Computer Security In computer security, AAA protocol commonly stands for authentication, authorization and accounting. - ppt download